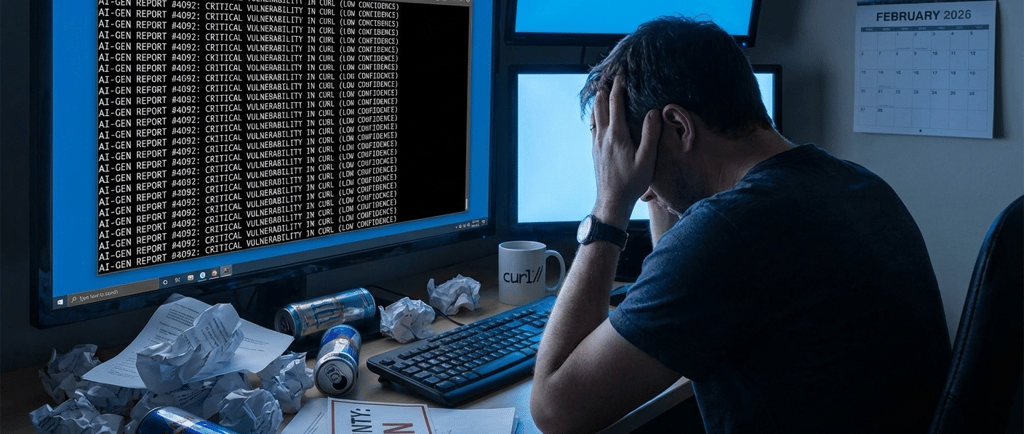
cURL ends bug-bounty programme after flood of “AI slop” security reports
The curl project has ended its bug bounty programme, with maintainer Daniel Stenberg citing an influx of low-quality “AI slop” security reports that drained maintainer time and attention. The project will still accept disclosures via private reporting routes, but without monetary rewards—prompting fresh debate about how bug bounties work in an era where convincing-looking reports are cheap to generate, but expensive to verify.
5 min read
The curl project has ended its long-running bug-bounty programme, with maintainer Daniel Stenberg saying the scheme has been overwhelmed by a growing volume of low-quality, sometimes fabricated “vulnerability” submissions — many of which appear to be AI-generated. The bounty officially stopped on 31 January 2026, and curl is shifting security reporting away from HackerOne towards private disclosure routes.
Why this matters
curl isn’t just “another open-source tool”. It’s the command-line utility (and associated library) that sits underneath a huge amount of routine internet plumbing — from development workflows to embedded systems to enterprise software. Security programmes like bug bounties are meant to be one of the ways that modern software ecosystems convert “good eyes” into real fixes. So when a project this widely used decides the bounty model is doing more harm than good, it becomes a signal flare for the rest of the security and open-source world.
This story is also about incentives: as generative AI makes it cheap to produce convincing-looking technical write-ups, the limiting factor becomes human verification time — and for many open-source projects, that time is painfully scarce.
What curl changed — and when
The decision unfolded in a way that’s now common in open source: it surfaced first through documentation changes and public discussion, then through a formal maintainer statement.
Mid-January 2026: observers noticed updates indicating curl would stop the bug bounty at the end of the month, alongside discussion of low-quality submissions.
22 January 2026: reporting linked the change to a surge in “AI slop” submissions and described updates removing bounty references from curl’s bug-bounty documentation.
26 January 2026: Stenberg published a detailed explanation confirming the programme was ending. He stated the bug bounty officially stops on 31 January 2026.
From February, curl’s position is simple: no rewards, no assistance to obtain compensation elsewhere, and security reports should use the project’s own disclosure routes (including private reporting on GitHub).
The core reason: “AI slop” and verification overload
Stenberg’s central argument is not “security reports are bad”. It’s that the signal-to-noise ratio collapsed — and the bounty created an incentive structure that rewards volume and persuasion rather than reproducible security impact.
Across coverage and his own writing, the recurring theme is that many submissions:
look plausible at first glance,
contain dense technical language, pseudo-exploit narratives, or code snippets,
but don’t reproduce as a real vulnerability when checked.
Some reporting highlights the scale of the problem in early 2026: Stenberg described receiving seven submissions within a sixteen-hour window, and counting twenty submissions already in 2026, with time spent handling them — yet ultimately concluding they did not identify a vulnerability.
That “handling time” isn’t just reading an email. Security reports demand careful triage: reproduce conditions, confirm behaviour, evaluate exploitability, check versions, assess impact, coordinate disclosure, and avoid false alarms that could cause unnecessary downstream disruption. In small open-source teams, that workload is multiplied by review norms — and curl has previously described its security team as small enough that each report can engage multiple people.
A programme that worked — until it didn’t
curl’s bug bounty began in April 2019, and for several years Stenberg describes it as effective and “quite successful”.
In July 2025 — months before the programme ended — Stenberg wrote that the bounty had delivered 81 genuine security problems and paid over $90,000 in awards at that point, but warned that low-quality “slop” reports were becoming a serious threat to the team’s sanity and time.
By January 2026, he reports updated lifetime figures: 87 confirmed vulnerabilities and over $100,000 paid out — but with the quality trend moving sharply in the wrong direction.
That arc matters: this wasn’t a bounty that “never worked”. It’s a programme that — in curl’s telling — delivered meaningful security outcomes, then became progressively harder to sustain as the incentive model began pulling in a flood of low-effort submissions.
What replaces the bounty: disclosure without payment
The end of the bounty is not the end of vulnerability reporting. It’s a change in process and incentives.
Stenberg says curl will still value security reports, but no longer offers rewards, and won’t help researchers obtain rewards from third parties.
Reporting also notes a shift away from the bounty platform channel and toward GitHub-based private vulnerability reporting and other direct routes.
This is a key point for readers who don’t live inside security policy: curl is not saying “stop reporting vulnerabilities”. It is saying “stop reporting them through a paid bounty funnel that has become a magnet for junk”.
The wider context: AI, bug bounties, and the “cheap text” problem
Security teams across the industry have been warning about an AI-driven increase in volume: more write-ups, more “possible issues”, more automated scanning output — not all of it useful. One industry response has been to introduce AI-assisted triage, with bounty platforms exploring mixed human/AI approaches to detect duplicates and prioritise credible reports.
But curl’s experience highlights a hard reality: even if AI can help generate reports, and even if platforms can use AI to pre-filter them, the final cost centre is still human verification — especially when the content is crafted to look high confidence.
That’s why this story is resonating beyond curl. It’s not just “a maintainer got annoyed.” It’s a case study in what happens when:
generation is cheap,
incentives reward quantity, and
verification remains expensive.
What happens next — and what to watch
There are a few practical questions this decision raises, and they matter for both security researchers and downstream users of curl:
1) Will ending payment reduce junk submissions?
That is curl’s stated hope: remove the incentive, reduce the volume.
But some observers are sceptical that the slop stops entirely — it may simply move channels (e.g., from bounty platforms to security@ inboxes), shifting rather than solving the workload. That’s one reason curl’s move toward controlled disclosure routes will be closely watched.
2) Will high-quality reporting drop as well?
Bug bounties exist partly because they compensate time. Removing rewards can reduce motivation for some researchers, especially those who do this as paid work. curl’s position is that valued reporters will still report serious issues, but the “future will tell.”
3) Will other open-source projects follow?
Several outlets have framed curl as an early, visible example of a broader pattern: open-source teams struggling to triage escalating volumes of questionable submissions.
If more projects conclude that bounty incentives are pulling in too much noise, the industry may see a shift toward alternative models: curated invite-only bounties, paid triage services, stronger reporter verification, or “deposit” systems that discourage low-effort spam.
4) What changes in curl releases?
curl’s own developer-facing notes show the bounty documentation change as part of ongoing project updates, with future release planning continuing as normal.
That’s an important signal: the bounty is ending, but development and maintenance are not.
Bottom line
curl’s decision is a warning that the security ecosystem can be broken not only by exploits, but by attention collapse: when “possible vulnerabilities” become abundant, the scarce resource becomes human review — and small teams can be drowned by plausible-sounding nonsense.
For curl, the fix is blunt: remove the bounty incentive, route disclosures through private reporting, and keep encouraging real vulnerability reports — just without paying for them.
If the change successfully reduces noise while preserving high-quality disclosures, it may become a template for other open-source projects trying to survive the new economics of AI-generated content.

Contact
Subscribe to our newsletter
Stay informed with global news updates on our main site
www.worldpressfreedom.com
© 2012 - 2026 WPF News
Michael Bosworth, Founder,
CEO & Chief Content Officer
